Enterprise AI coding doesn’t have to be all or nothing
Across the industry, engineering teams are embracing AI coding tools and seeing real results. Faster refactors. Better test coverage. Quicker turnaround on features. Organizations that have gone all-in on AI-assisted development are shipping faster than ever, and the gap between them and everyone else is widening.
Enterprise teams see this happening. They want that same velocity. But they also sit on codebases full of proprietary business logic, internal architecture, customer data flows cannot leave controlled boundaries. Security says no. Compliance says no. And honestly, they are right to say no.
So developers do what they can: copy a few functions into a chat window, rename some symbols by hand, paste the output back, and hope nothing sensitive slipped through. It works, sort of, but it is slow, inconsistent, and impossible to audit.
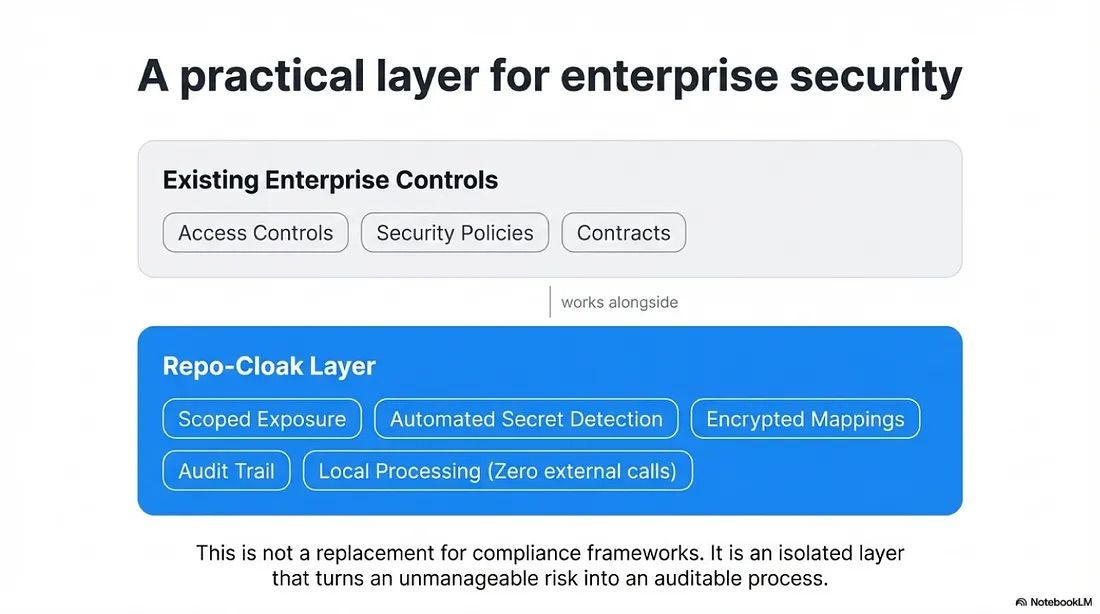
The result is a frustrating middle ground. Teams that fully block AI tools lose velocity and risk frustration. Teams that fully embrace AI tools without guardrails take on exposure they may not fully understand. Neither extreme works well for organizations that need both speed and control.
What if there was a middle path?
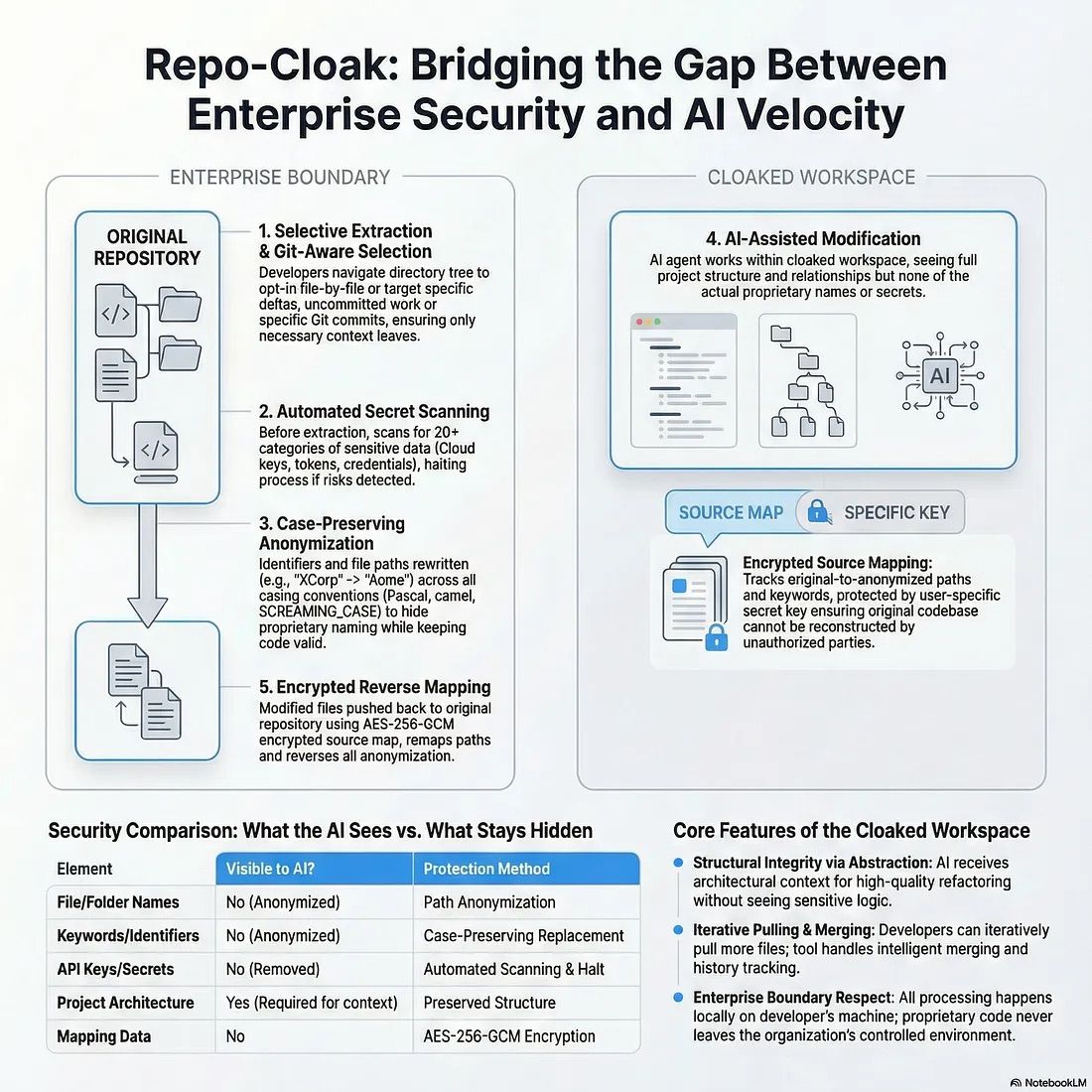
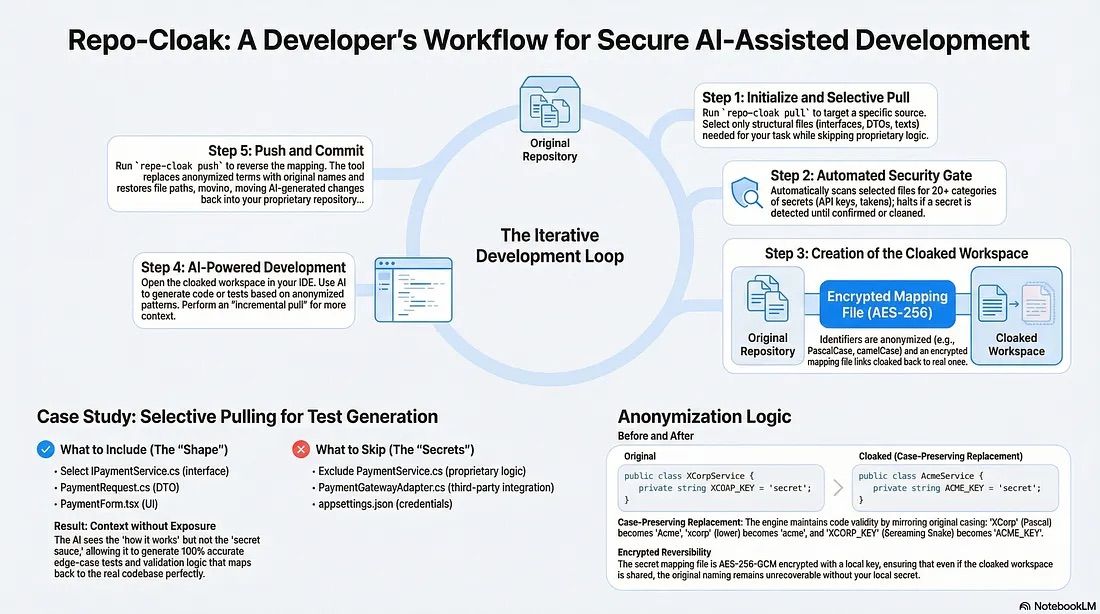
This article explores one such approach, where developers work with AI on anonymized abstractions of their codebase rather than the real thing. AI gets the structural context it needs to produce high-quality output. The proprietary code, the real names, and the secrets never leave the building. And the changes push back cleanly into the original repository, as if AI had been working on the real codebase all along.
Why AI needs more than snippets
AI coding assistants produce dramatically better results when they see real project structure. Hand them a single isolated function, and the output is generic. Hand them a realistic project slice with folder hierarchies, dependency relationships, and naming conventions, and the results transform: meaningful refactors, accurate test generation, pattern-aware code scaffolding.
But realistic project slices contain exactly what enterprises protect most carefully.
The key insight is this: AI does not actually need the proprietary code itself. It needs the structure, patterns, and relationships to reason about. If you can give AI a project that looks and behaves like the real thing architecturally, but with all identifying details swapped out, it can still produce excellent work. And that work can be mapped straight back into the original codebase.
That is the core idea behind Repo-Cloak, an open-source CLI tool that creates anonymized workspaces from enterprise codebases.
How it works
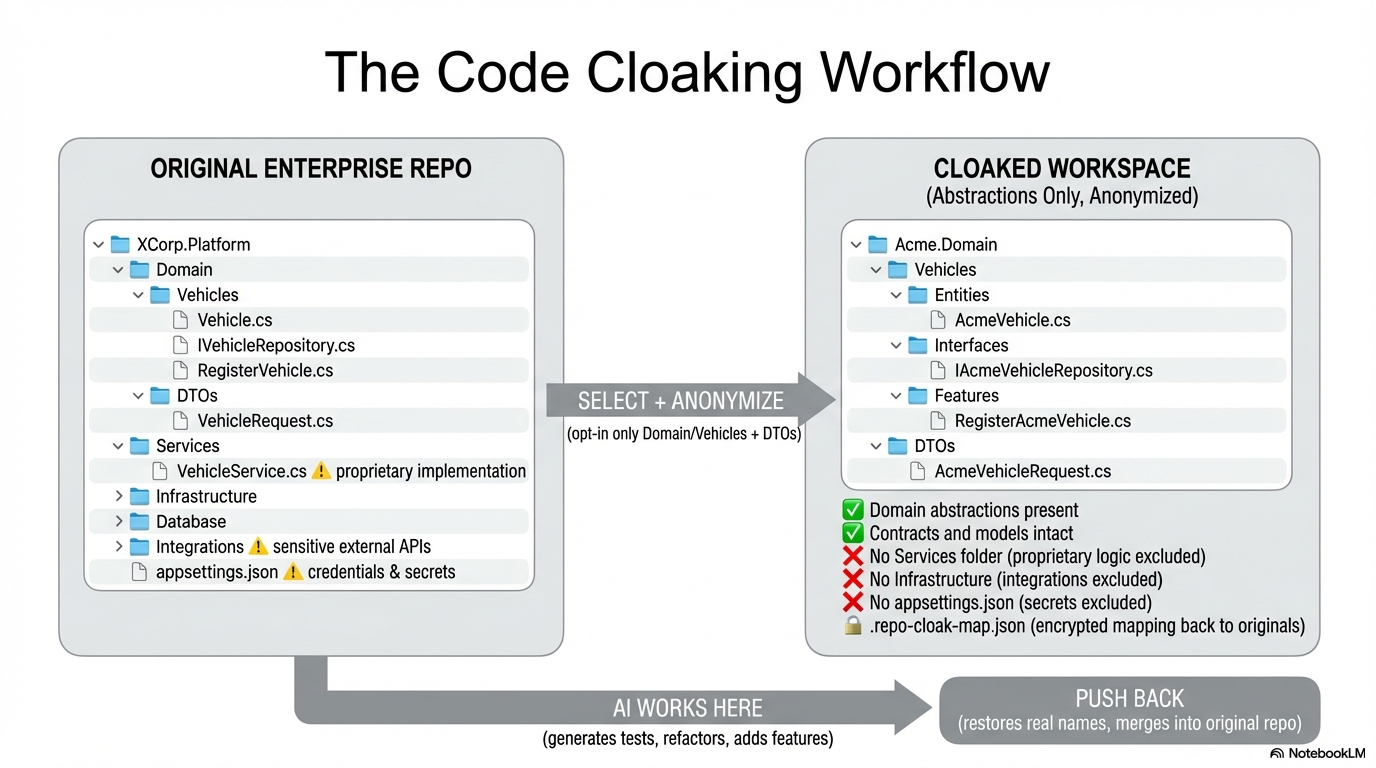
Rather than giving AI tools direct access to source control, you create a deliberate boundary: a cloaked workspace that contains only the files you choose, with identifiers anonymized and secrets caught before anything crosses the line.
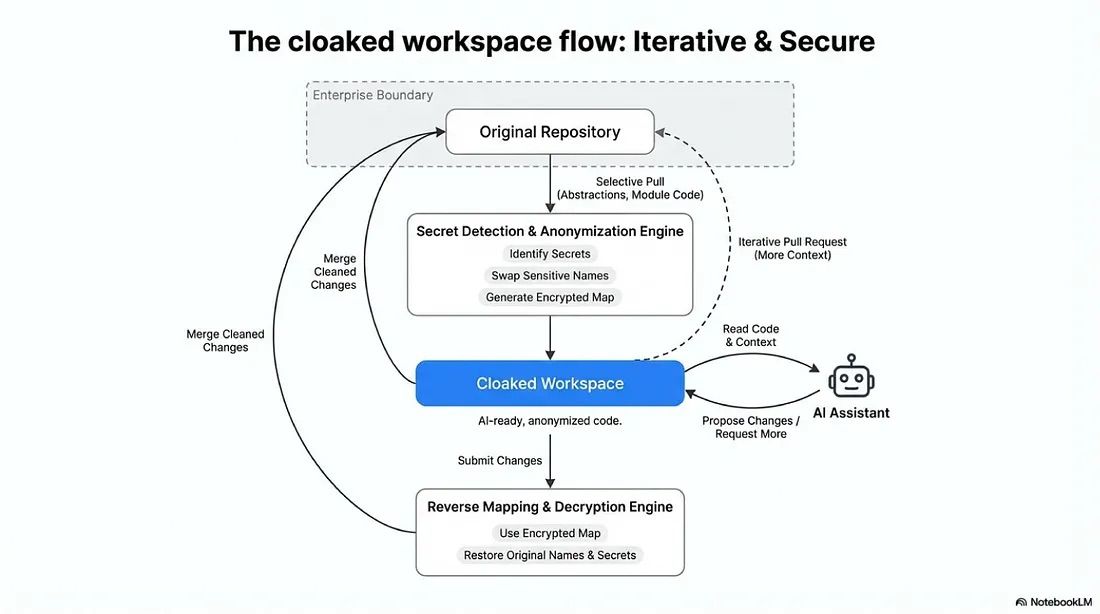
From the AI’s perspective, this is just another project to work on. From the organization’s perspective, the proprietary code never left. Only its anonymized abstraction did.
Giving AI the right context, nothing more.
Smart file selection
Nothing leaves the repository boundary unless you explicitly choose it. You navigate the directory tree and opt in, file by file. For teams using Git, this gets even sharper:
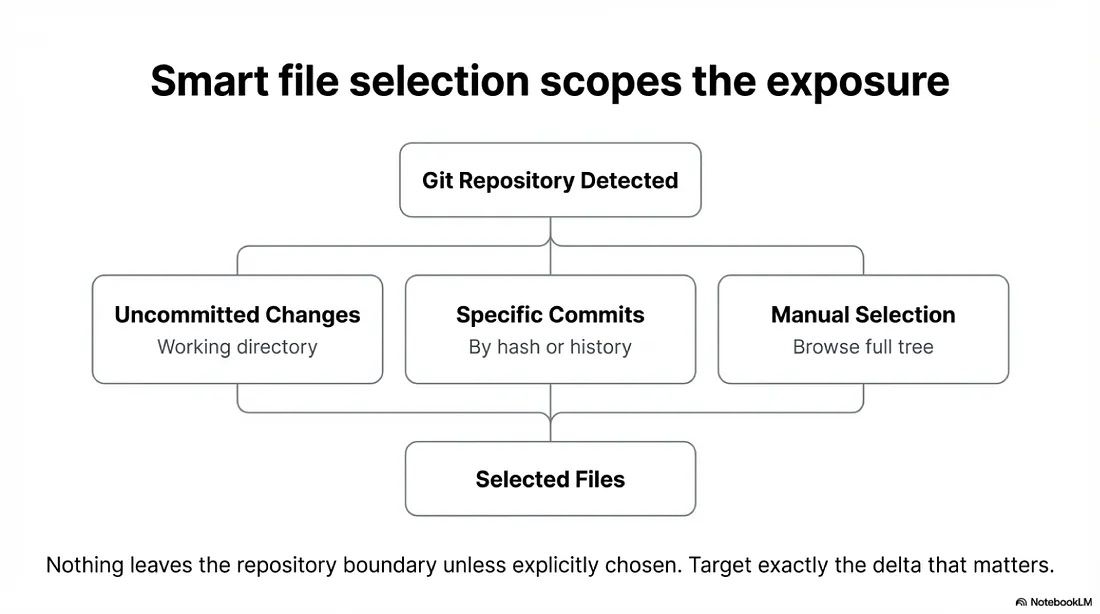
You can target a specific commit, select from recent history, or pull only uncommitted work. AI assistance gets scoped to exactly the delta that matters, not the entire codebase.
Anonymization that preserves structure
This is the piece that makes the approach practical. Identifiers get rewritten, but the project structure stays architecturally identical. AI sees real folder hierarchies, real dependency relationships, real naming patterns & abstractions. It just does not see your names.
A sample workflow: generating test cases without exposing business logic
To see how this plays out in practice, consider a common scenario.
A developer on an enterprise team needs comprehensive test coverage for a payment processing module. The business logic inside the service layer is proprietary, but the interfaces, abstractions, and frontend forms that interact with it are not. They contain no trade secrets. They just define the shape of the system.
Here is how the workflow looks:
The AI never saw the payment processing logic, the gateway integration, or the credentials. It only saw the abstractions, the shapes, and the patterns. And that was enough to generate meaningful, production-quality test coverage.
This same approach works for other scenarios: generating API documentation from controller signatures, scaffolding new features based on existing patterns, or exploring refactoring strategies across a service boundary. The developer always controls what goes in, and the proprietary core stays untouched.
Pushing changes back
This is where the approach pays off. AI generates code against the anonymized workspace. When that work is ready to come home, the mapping (AES-256 encrypted, tied to a local key) reverses every replacement, remaps file paths, and deposits the modified files cleanly into the original repository.
The result is a conventional changeset, ready for code review and testing, as if AI had been working on the real codebase directly. Except it never was.
Where this fits
Finding the balance
Some organizations are going all-in on AI and seeing massive returns. Others have locked it out entirely, and their developers feel it every day. Most enterprise teams sit somewhere in between, wanting the efficiency but unsure how to get there without the risk.
This approach offers one way to find that balance. It is not the only way, and it is not a silver bullet. But it turns an all-or-nothing decision into something more nuanced: “Which parts of our codebase can benefit from AI assistance, and how do we expose them safely?”
The codebase stays in its guarded world. The developers get the productivity boost that modern tooling delivers.
Repo-Cloak is open source and available on npm.
Contributions and thoughts are highly welcome.
